vRealize Automation (vRA) 8.3 GA
vRealize Automation 8.3 is out. There are a number of exciting changes included. These are my top picks from them.

Late last night was the GA (general availability) of vRA 8.3. As it's in my wheelhouse it's probably one of the few GA announcements that I tend to write about.
In this brief post I'll mention a couple of the changes that interest me the most. For the full list of what's new or updated, it's probably best to go read the release notes and try it out in your lab. Here's a couple of links:


SaltStack Config
SaltStack Config (or, vRealize Automation SaltStack Config, to give it its full name) has to be one of the biggest additions. When you head in to Lifecycle Manager you'll see that the product support pack for the 8.3 release includes SSC:
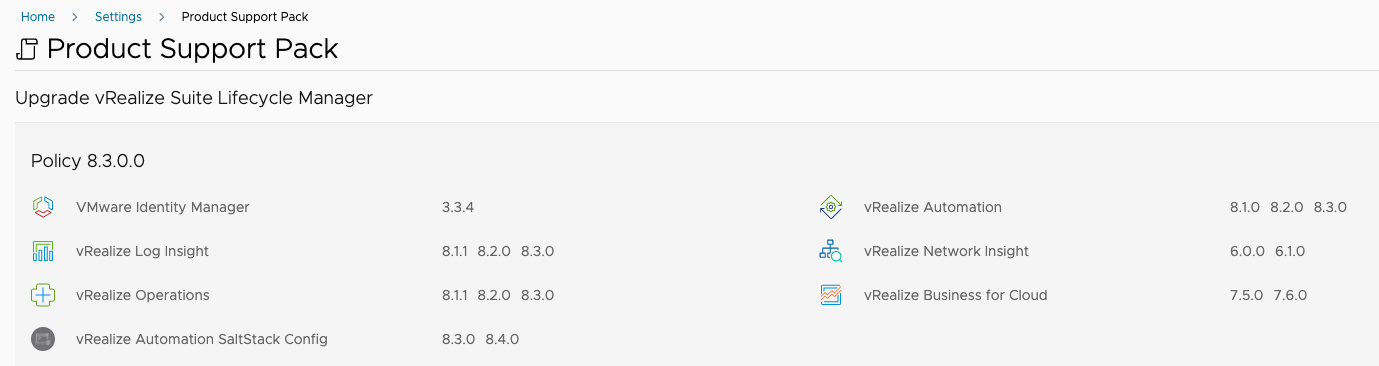
What's more, you can deploy SSC through LCM as you can the other products, and it's based on a Photon OS OVA now too. It's on a per-tenant basis, so if you have multiple tenants then each will get their own SSC deployment.
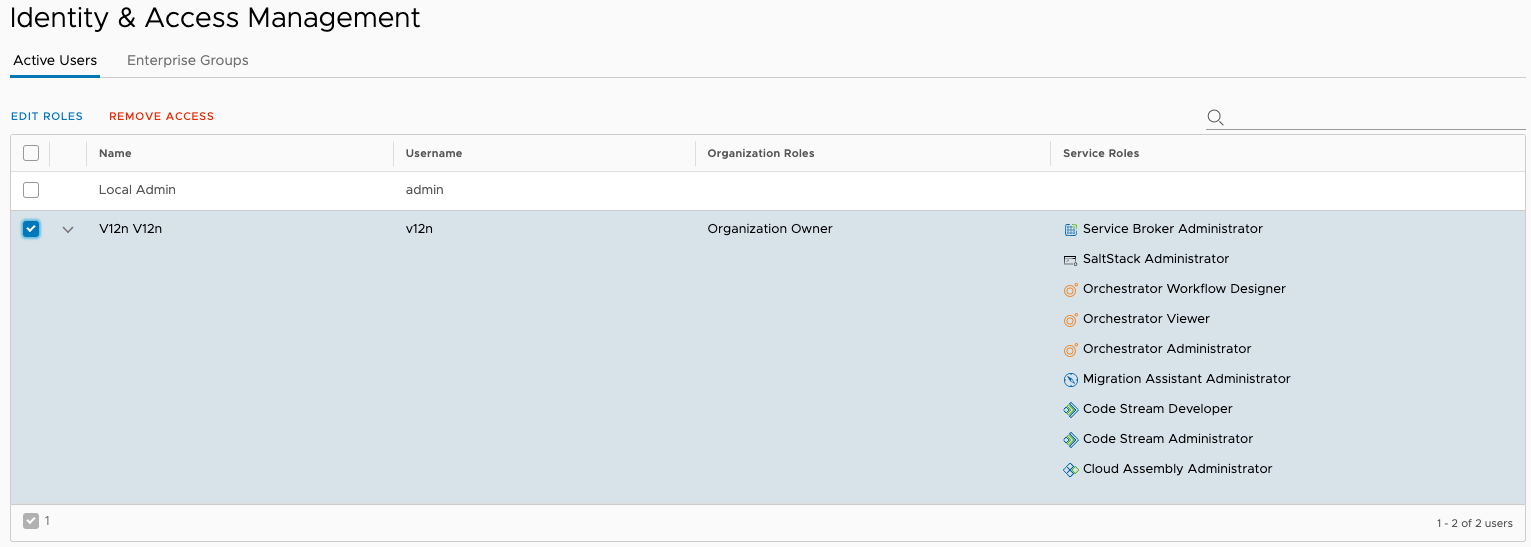
There's also a new organization role available - "SaltStack Administrator":
But that's not all! The CMBU (Cloud Management Business Unit) technical marketing team has created a Salt module for vRA. It's available (for free) from Github:
The recommended approach for installing the Salt Minion on workloads is to use the bootstrap script (see https://bootstrap.saltstack.com) which can easily be executed through the use of cloud-init. And... you can specify the master address to be used through a Property Group.
Property Groups
We had these in vRA 7.x, and now they're in vRA 8.3 and will make standardisation across Cloud Templates easier.
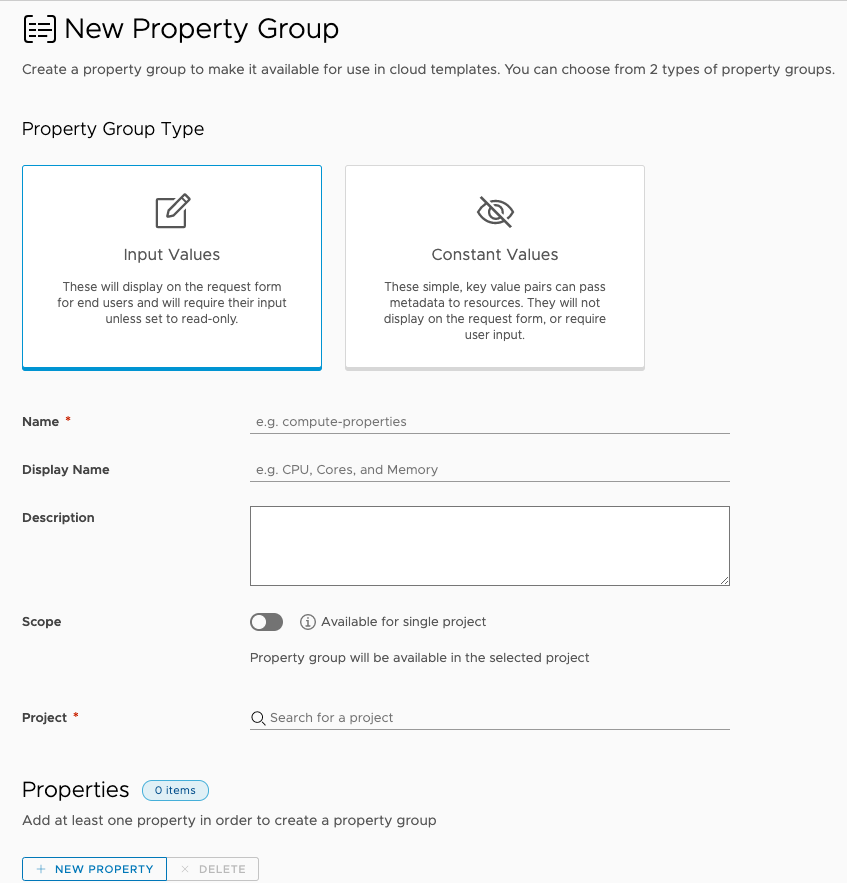
Property groups are created from under the Design menu and can be specific to a project or available to all projects. As the example text shows, you could define a group for compute-properties that you would then reference in a Cloud Template as follows:
Secrets
How often have you created a Cloud Template and ended up having to stick some sort of value or data in there that you'd rather wasn't easily visible or shared? Well now you can keep them secret.
Secret values are new to vRA 8.3 and allow for passwords, license keys, SSH keys etc to be stored away from prying eyes. They're created from a new option under the Infrastructure menu and associated with a project. (That association is strict though, a secret created for one project is not visible to another project.)
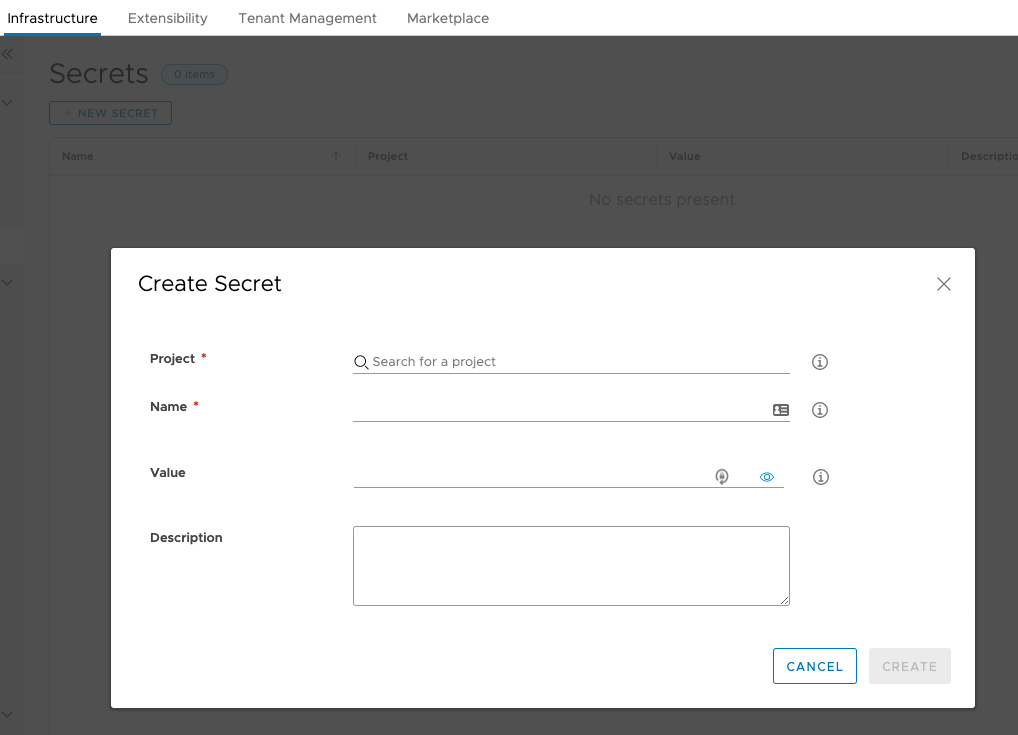
Secrets can be consumed in Cloud Templates, for example:
'${secret.ssh_public_key}'
Which would return the value of the secret named "ssh_public_key". Secrets can also be consumed in ABX actions. Let's say you had an encrypted on your Cloud Template that placed a root password as a property on a Cloud.Machine object that you then wanted to pass to some other system via an ABX action. Well, you'd retrieve the value using something like the following:
variable = context.getSecret(inputs["customProperties"]["rootPassword"])
Other Stuff
There are lots of other enhancements, too many to mention here. But I'll be experimenting with them over the coming weeks. I'm already working with SaltStack so it's great to see that and vRA getting to know each other better.
