The importance of applying software updates
Are we conditioned by our smart phones to assume that security is taken care of automatically? When it comes to business and enterprise software it's best to stay on top of updates.

Read the release notes for any application or piece of software and at some point you'll notice a reference to some "security updates". In some cases you'll even see references to specific, documented security vulnerabilities.
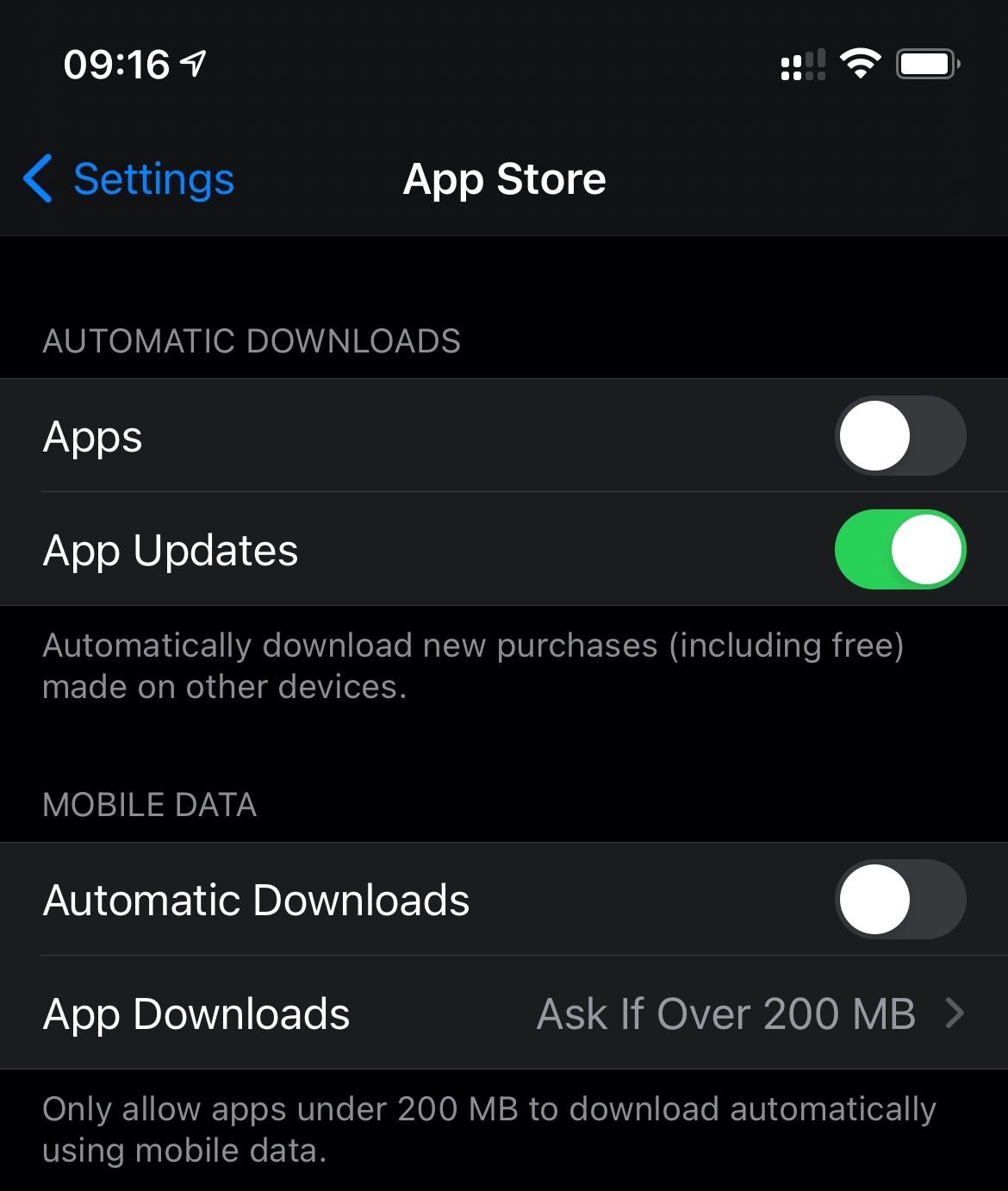
Sometimes we're too focussed on the new and improved features to think about security updates. We've been conditioned by modern technology to think that it all happens automatically...
...or we're too distracted by the hundreds of things clammouring for our attention that we don't have the headspace to give security a thought.
Of course, there's a difference between your favourite social media app being unavailable for 90 seconds whilst it updates and applying firmware updates to an enterprise grade server that makes one or more business critical services go offline for an hour. One costs you 90 seconds of your time and probably won't matter too much if it goes wrong. But both are important enough that they should be executed regularly.
VMware's solutions are no exception to the requirement for updates. Software is written by humans (who can be fallable) and will inevitably contain vulnerabilities from time to time. The two most important things you can do are:
- Visit the VMware Security Advisories page. Here you'll find all of the security advisories related to any vulnerabilities that have been reported or fixed. You can also subscribe to get email updates.
As an example, CVE-2019-5544 and CVE-2020-3992 have been exploited a number of times. Fixes are available though, as is a KB article that covers mitigating the vulnerability. - Make sure that you have an established process that covers checking for and applying updates to your infrastructure on a regular cadence.
Some vulnerabilities get more publicity than others, usually when they're actually exploited and cause harm, or it's a slow news day. And in some cases it can be weeks or months after fixes are available. The best defense against vulnerabilities though is applying regular updates though and it should be a foundation of your security policy.
